| Google boosts security with physical keys |
Google already offers security precautions like two-step authentication, which provides additional protection by requiring you to enter not only your password but also a one-time code received by SMS or similar. This is a crucial weapon in the fight against hackers, since weak usernames and passwords are still be the primary reason for accounts being breached. Security Keys now take things one step further, strengthening your Google Drive account’s coat of armor to an even greater extent. The Security Key is a physical USB device that is plugged into your computer, and which sends an encrypted signature, instead of a password or other code, to verify your identity and permit you access to your Google account. Crucially, Security Keys are inexpensive – starting from around $6 per unit – and require no additional software for deployment, use or management. Administrators have the ability to track when and where each key is used, as well as being able to disable them if lost and issue backup codes to allow staff uninterrupted access even if they do misplace their key. Simplifying the login process is also a key part of what Google has tried to achieve with Security Keys. To that end, the first time you use your key to access your Google account on a particular computer, you can opt for Google to remember that device. On subsequent occasions you can quickly sign in using only your password, and without requiring either your key or a two-step authentication code. You can still sign in using your key on other machines, and if a hacker tries to access your account without your key they will also be prompted for a two-step verification code (which, unless they have access to your cell phone, they shouldn’t be able to provide). Security Keys aren’t an entirely perfect solution, though – there are some significant limitations to the technology. For one, you can’t use them on mobile devices, since they require a USB port to work, and they only allow you to access your Google account through the Chrome browser. Windows, Mac OS, ChromeOS and Linux operating systems are all supported, but if you’re working from your phone or on a browser other than Chrome then you’ll need to continue using two-step authentication. Google says you can mix and match different methods of verification, opting to use Security Keys where they are supported and two-step verification otherwise (or if you don’t have your key with you). What’s more, only Google Drive currently supports Security Keys – it’s not yet possible to use them with Google Apps, for example. But, while the technology is primarily targeted at Google Drive for Work users, it’s possible to link a single key to multiple accounts, meaning you can use it to access both your work and personal Google accounts. Some users have also queried how much of a safeguard the technology really provides in the absence of an additional PIN code or fingerprint authentication being required for activation, suggesting that a stolen Security Key could be used to access a computer that a user has previously asked Google to remember. But Security Keys do appear to offer at least some additional protection, which will be of comfort to businesses handling sensitive data. Give us a call to find out how to employ Security Keys and other technology solutions to bolster your protection against network intrusion and data breaches. Published with permission from TechAdvisory.org. Source.
|
| How to advertise on Facebook: the basics |
|
| How to backup your data |
|
| Stay productive when working remotely |
|

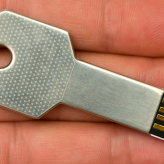 If your business is lacking adequate security protection, the doors are wide open to an attack from outside. To make things worse, security threats are constantly evolving and developing, rendering them more difficult to keep up with. At least Google is on your side – its recent introduction of physical Security Keys for Drive for Work users means an extra layer of safeguarding for the cloud-based data files you rely on to power your organization.
If your business is lacking adequate security protection, the doors are wide open to an attack from outside. To make things worse, security threats are constantly evolving and developing, rendering them more difficult to keep up with. At least Google is on your side – its recent introduction of physical Security Keys for Drive for Work users means an extra layer of safeguarding for the cloud-based data files you rely on to power your organization.
 Businesses today are relying on data to run their day-to-day operations. We use it to build client relationships, generate sales reports, develop marketing strategies, and so much more. But if something were to happen to it, a devastating disaster for example, you could risk losing your whole business if you haven’t properly backed up. With that in mind you should take necessary precautions to protect your data in the event of a crisis. Let’s take a look at some devices you can use to keep your information out of harm’s way.
Businesses today are relying on data to run their day-to-day operations. We use it to build client relationships, generate sales reports, develop marketing strategies, and so much more. But if something were to happen to it, a devastating disaster for example, you could risk losing your whole business if you haven’t properly backed up. With that in mind you should take necessary precautions to protect your data in the event of a crisis. Let’s take a look at some devices you can use to keep your information out of harm’s way. When many people think of remote working, they imagine a person lounging on the couch in their pajamas with a laptop. Does this vision stir up images of productivity? We doubt it. That’s why it’s important to instill the proper habits of a work-from-home culture into your remote workers’ minds. Here are a few principles every employee should consider when working remotely.
When many people think of remote working, they imagine a person lounging on the couch in their pajamas with a laptop. Does this vision stir up images of productivity? We doubt it. That’s why it’s important to instill the proper habits of a work-from-home culture into your remote workers’ minds. Here are a few principles every employee should consider when working remotely.